“Join the tide. Every exposure, every disengagement from their parasitic system, every communication of truth, every civil disobedience helps build the crescendo of Truth sweeping the planet. We can take them down. Their structure is a fabrication, an overlay on human consciousness, and it cannot survive without our cooperation.” Z Gardner
 As America continues to be overwhelmed by an obviously orchestrated mass intrusion of immigrants over its borders, the utter hypocrisy of increasingly stringent so-called “security measures” for the rest of the population paints a very clear picture.
As America continues to be overwhelmed by an obviously orchestrated mass intrusion of immigrants over its borders, the utter hypocrisy of increasingly stringent so-called “security measures” for the rest of the population paints a very clear picture.
There is no terrorism threat to the United States. It’s bogus now and has been completely fraudulent from the get go.
If there were such a threat, not only would this flood of illegals not be allowed never mind clearly encouraged, but anyone crossing the border would have to undergo the same rigorous Orwellian strip downs, x-rays, inspections and interrogations normal citizens are subjected to. On top of that, once they are herded over the border they are being given escorts to safe havens including military bases, given supplies and free transportation to destinations around the country, and are in line for free health care, legal representation and a plethora of other benefits that will no doubt prove back-breaking to the American economy and way of life.
All by design, while cardboard cut-out Obama, the human decoy, takes his multi-million dollar 2-week summer vacation at swishy Martha’s Vineyard. Get the picture? There’s no concern because they are transparently behind it. Besides, while the stage prop Obama is away the real rulers in the shadows can have a field day without having to worry about programming their mouthpiece. Hence all the “vacations” for this vapid useful idiot.
The Set Up – Destruction, Division, the NAU and False Flag Fuel
Continue reading →
 Rex Santus – Something strange is happening at the Sunspot Solar Observatory in New Mexico, and there’s only one thing we know for certain: It’s not not an alien.
Rex Santus – Something strange is happening at the Sunspot Solar Observatory in New Mexico, and there’s only one thing we know for certain: It’s not not an alien.
 As America continues to be overwhelmed by an obviously orchestrated mass intrusion of immigrants over its borders, the utter hypocrisy of increasingly stringent so-called “security measures” for the rest of the population paints a very clear picture.
As America continues to be overwhelmed by an obviously orchestrated mass intrusion of immigrants over its borders, the utter hypocrisy of increasingly stringent so-called “security measures” for the rest of the population paints a very clear picture. The First Amendment to the Constitution
The First Amendment to the Constitution 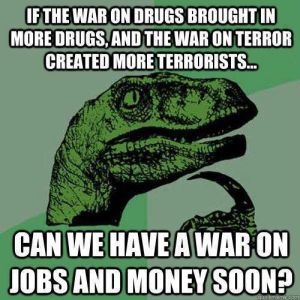 Empires – almost by definition – fight imperial wars to gain land and resources.
Empires – almost by definition – fight imperial wars to gain land and resources.